
Imagine waking up one morning to find your website defaced, your customer information stolen, and your online reputation shattered. The aftermath of a successful hacking attempt can be devastating, not only in terms of financial loss but also in the erosion of trust among your customers. So how can we protect your website from hackers?
The unfortunate reality is that cybercriminals are constantly devising new techniques to exploit vulnerabilities and gain unauthorized access to websites, causing significant harm to businesses and their customers.
However, by implementing these 8 security measures, you can fortify your website’s defenses and protect your digital assets from falling into the wrong hands.
1. Install Security Plugins and Software
Websites serve as gateways to businesses and personal information and protecting your website from hackers should be a top priority. While the prospect of securing your website might sound daunting, there are simple yet effective steps you can take to fortify your online fortress.
One such step is to install security plugins, particularly if your website is built on a content management system (CMS) like WordPress, Magento, or Joomla. These CMS platforms offer a wide range of security plugins that actively ward off hacking attempts and strengthen your website’s defense mechanisms.
For WordPress users, popular security plugins like iThemes Security, Bulletproof Security, and Wordfence offer comprehensive protection against common vulnerabilities. Magento users can consider utilizing security options such as Amasty and Watchlog Pro, while Joomla users can explore extensions like JHacker Watch and RSFirewall. These plugins address inherent security weaknesses within each platform and act as an additional shield against potential threats.
2. Embrace HTTPS for Secure Data Transmission
Safeguarding sensitive information shared on your website is of paramount importance. Users expect a secure browsing experience, and one way to provide it is by implementing HTTPS (Hypertext Transfer Protocol Secure) on your website.
HTTPS ensures secure data transmission between your website and the server by encrypting the information exchanged. It adds an extra layer of protection, especially when users provide sensitive data like credit card details, personal information, or login credentials.
Previously, HTTPS was primarily associated with e-commerce websites. However, its importance has now extended to all types of websites. In fact, major search engines like Google prioritize websites with HTTPS in search results, making it crucial for better visibility and trustworthiness.
Implementing HTTPS requires an SSL (Secure Sockets Layer) certificate, which verifies the authenticity of your website and encrypts the data transmitted. While SSL certificates were once considered an additional expense, they are now more accessible and often included as part of web hosting packages.
At HostGator or SiteGround, for example, web hosting packages come with a free SSL certificate, making it easier for website owners to secure their sites. By obtaining an SSL certificate and enabling HTTPS, you not only protect user data but also enhance your website’s credibility and trustworthiness, which may help to push your website’s ranking.
3. Regularly Update Your Website Platform and Software
Content management systems (CMS) and other website components often release updates that address security vulnerabilities and patch potential loopholes that hackers may exploit.
Vulnerabilities in CMS platforms and their extensions/plugins are among the leading causes of website infections. As open-source software, their code is accessible not only to well-intentioned developers but also to malicious hackers who can scrutinize it for weaknesses.
To protect your website from potential attacks, make it a priority to regularly update your CMS, plugins, apps, and any other software or scripts you’ve installed. Staying up to date with the latest versions ensures that you benefit from security patches and fixes provided by the developers.
If your website is built on a popular CMS like WordPress, checking for updates is relatively simple. When you log into your WordPress dashboard, you’ll find an update icon next to your site name in the top left corner. By clicking on the number, you can access the WordPress Updates page and easily update your website.
4. Strengthen Your Password Security
While it may sound simple, maintaining strong and secure passwords is a fundamental aspect of website security. Weak passwords are an open invitation for hackers to gain unauthorized access to your website and potentially wreak havoc on your online presence.
To fortify your password security, consider the following measures:
Create Complex and Unique Passwords:
Avoid using easily guessable passwords like “123456” or common phrases. Instead, develop passwords that are long, include a mix of uppercase and lowercase letters, numbers, and special characters. The more complex and unique your passwords are, the harder they are for hackers to crack.
Use Password Generators:
If you struggle to come up with strong passwords, consider using password generator tools available online or built into reputable password management software. These tools can create highly secure passwords that are challenging to guess.
Avoid Personal Information:
Steer clear of incorporating personal information such as your name, birthdate, or address in your passwords. Hackers can easily find such details and exploit them to gain unauthorized access.
Implement Two-Factor Authentication (2FA):
Enable two-factor authentication for your website whenever possible. This adds an extra layer of security by requiring users to provide a second form of verification, such as a unique code sent to their mobile device, in addition to their password.
Regularly Update and Rotate Passwords:
It’s essential to change your passwords periodically. Set a reminder to update your passwords every few months or whenever there’s a potential security breach. Avoid reusing passwords across multiple accounts to minimize the impact if one account is compromised.
Educate Your Team:
If you have a team managing your website, ensure that everyone understands the importance of password security. Implement password policies that encourage strong passwords and educate your team members about best practices for password management.
5. Invest in Regular Website Backups
No matter how many security measures you implement, there is always a potential risk of a website compromise or data loss due to unforeseen circumstances. That’s why it’s crucial to invest in regular website backups as part of your overall security strategy.
Here’s why website backups are essential and how you can ensure their effectiveness:
Protection against Data Loss
Website backups act as a safety net in case of accidental deletion, hardware failure, software errors, or even malicious activities such as hacking or malware attacks. With a recent backup in place, you can quickly restore your website to its previous state, minimizing downtime and potential data loss.
Comprehensive Backup Strategy:
Develop a comprehensive backup strategy that includes both files and databases. Regularly back up your website’s core files, themes, plugins, and any other customizations.
Automated Backup Solutions:
Utilize automated backup solutions to simplify the process and ensure regularity. Many web hosting providers offer built-in backup services or recommend reliable backup plugins or software. These tools allow you to schedule automatic backups at specified intervals, reducing the risk of forgetting to perform backups manually.
Off-Site Storage:
Store your backups in an off-site location or a secure cloud storage service. By keeping backups separate from your primary server, you mitigate the risk of losing both your website and its backups in the event of a server failure or physical damage.
Test Backup Restoration:
Regularly test the restoration process from your backups to ensure their integrity and usability. Performing restoration tests allows you to verify that the backup files are complete and functional, giving you confidence in your ability to recover your website if needed.
Retention Period:
Determine the appropriate retention period for your backups based on your website’s size and frequency of updates. Ideally, maintain multiple versions of backups, including recent copies as well as older ones. This provides flexibility in case you need to revert to a specific point in time.
6. Implement Strong User Authentication and Access Controls
One of the critical aspects of website security is ensuring that only authorized individuals have access to your website’s backend and sensitive information.
Here are some key practices to follow:
Unique Usernames and Strong Passwords
Encourage all users, including administrators and staff members, to create unique usernames and use strong, complex passwords. Strong passwords should include a combination of uppercase and lowercase letters, numbers, and special characters. Avoid using common passwords or easily guessable information such as birthdates or names.
Two-Factor Authentication (2FA):
Enable two-factor authentication for all user accounts whenever possible. 2FA adds an extra layer of security by requiring users to provide a second form of verification, such as a unique code sent to their mobile device, in addition to their username and password.
Role-Based Access Control (RBAC):
Implement RBAC to assign specific roles and permissions to different user accounts based on their responsibilities. This ensures that users only have access to the necessary features and data required for their job functions. Regularly review and update user roles and permissions as organizational needs change.
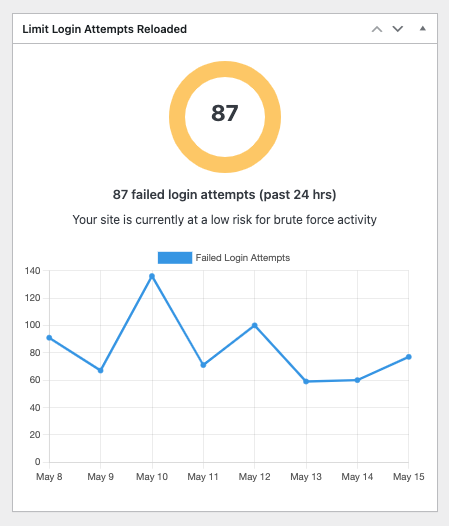
Account Lockout Policies:
Implement account lockout policies to prevent brute-force attacks, where hackers repeatedly attempt to guess usernames and passwords to gain unauthorized access. Configure your website’s login system to automatically lock accounts after a certain number of failed login attempts. This helps protect against unauthorized access.
Regularly Review User Accounts:
Regularly review and audit user accounts to identify and remove any inactive or unused accounts. This reduces the potential attack surface and helps maintain an up-to-date list of authorized users with access to your website.
Secure User Session Management:
Implement secure session management practices to ensure that user sessions are adequately protected. This includes enforcing session timeouts, requiring re-authentication for sensitive actions, and using secure session cookies.
Employee Training:
Educate your staff and users about the importance of strong user authentication and access controls. Train them to recognize potential security threats such as phishing attempts or social engineering techniques that could compromise their login credentials. Encourage regular password updates and provide resources for password management best practices.
7. Regularly Monitor and Review Website Logs
Website logs provide valuable information about user activities, server requests, error messages, and potential security threats. Here’s how to effectively monitor and review your website logs:
Enable Logging
Ensure that logging is enabled on your web server and relevant software applications. Enable logging for web server access logs, error logs, database logs, and any other pertinent logs specific to your website’s infrastructure.
Implement Log Management Tools:
Utilize log management tools or software solutions that can aggregate, analyze, and alert you to potential security issues. These tools can help you centralize logs from multiple sources, generate reports, and identify patterns or anomalies that may indicate malicious activity.
Regularly Review Logs
Set up a schedule to review your website logs on a regular basis. This could be daily, weekly, or monthly, depending on the volume of traffic and the nature of your website. Reviewing logs allows you to detect any suspicious activities, such as repeated failed login attempts, unusual access patterns, or unexpected system errors.
Analyze Error Logs:
Pay special attention to error logs, as they can provide insights into potential vulnerabilities or misconfigurations. Identify recurring errors or warning messages that could indicate attempts to exploit your website or server.
Monitor User Activities
Monitor and analyze user access logs to identify any suspicious behavior or unauthorized access attempts. Look for any unusual IP addresses, multiple login failures, or unusual activity patterns from specific user accounts.
Set up Alerts
Configure alerts or notifications within your log management tools to receive real-time notifications of critical events or potential security breaches. This ensures that you can respond promptly to any suspicious activity or threats.
You may also use different plugins depending on your CMS to help manage keep track of your logs.
Regularly Update and Patch:
Keep your web server software, content management system, plugins, and other components up to date with the latest security patches. Regular updates help address known vulnerabilities and reduce the risk of exploitation.
8. Implement Web Application Firewalls (WAF)
Web application firewalls (WAFs) act as a protective barrier between your website and potential threats. They help identify and filter out malicious traffic, providing an additional layer of security for your web applications. Consider the following when implementing a WAF:
Choose a Reliable WAF Solution:
Select a reputable and reliable WAF solution that suits your website’s needs. There are both cloud-based and on-premises WAF options available. Evaluate the features, scalability, performance, and support provided by different vendors to make an informed decision.
Enable OWASP Rulesets:
OWASP (Open Web Application Security Project) provides a set of rules and guidelines for securing web applications. Ensure that your WAF is configured to enable the appropriate OWASP rulesets. These rulesets help protect against common web application vulnerabilities, such as SQL injection, cross-site scripting (XSS), and remote file inclusion.
Customize WAF Rules:
Tailor the WAF rules to match your specific web application’s requirements. Customize the rules to allow legitimate traffic while blocking malicious requests. Regularly review and update the rules based on emerging threats and changes in your application’s functionality.
Implement Rate Limiting and IP Blocking:
Configure your WAF to enforce rate limiting rules and block IP addresses that exhibit suspicious behavior. Rate limiting prevents brute-force attacks, while IP blocking helps mitigate threats from known malicious sources.
Regularly Monitor WAF Logs:
Monitor the logs generated by your WAF to identify any unusual patterns or attacks. Analyze the logs for any potential security incidents or false positives. Implement alerts and notifications to promptly respond to suspicious activities.
Stay Up to Date with WAF Updates:
Keep your WAF solution up to date by installing the latest patches and updates. Regularly check for vendor releases and security advisories. Outdated WAF software may have vulnerabilities that attackers can exploit.
Test WAF Effectiveness:
Conduct periodic penetration testing and vulnerability assessments to evaluate the effectiveness of your WAF. Identify any gaps or weaknesses in the WAF configuration and address them promptly. Regular testing helps ensure that your WAF is providing the intended protection.
Final Thoughts
We understand the importance of safeguarding your online presence and are here to assist you every step of the way. If you encounter any security troubles or require professional assistance, don’t hesitate to reach out to us. Our team of experts is well-equipped to protect your website through comprehensive services like penetration testing and employee training. Stay proactive, prioritize security, and provide a safe digital experience for both yourself and your users.
Contact us today to fortify your defenses and ensure a secure online environment.


