Affected versions
ledgerhq/connect-kit 1.1.5
ledgerhq/connect-kit 1.1.6
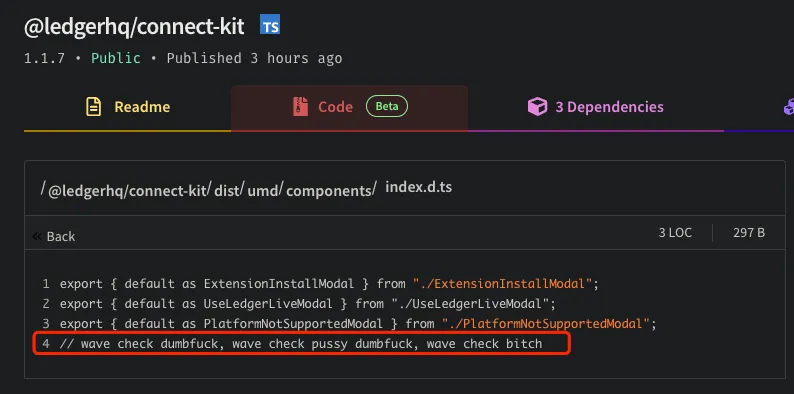
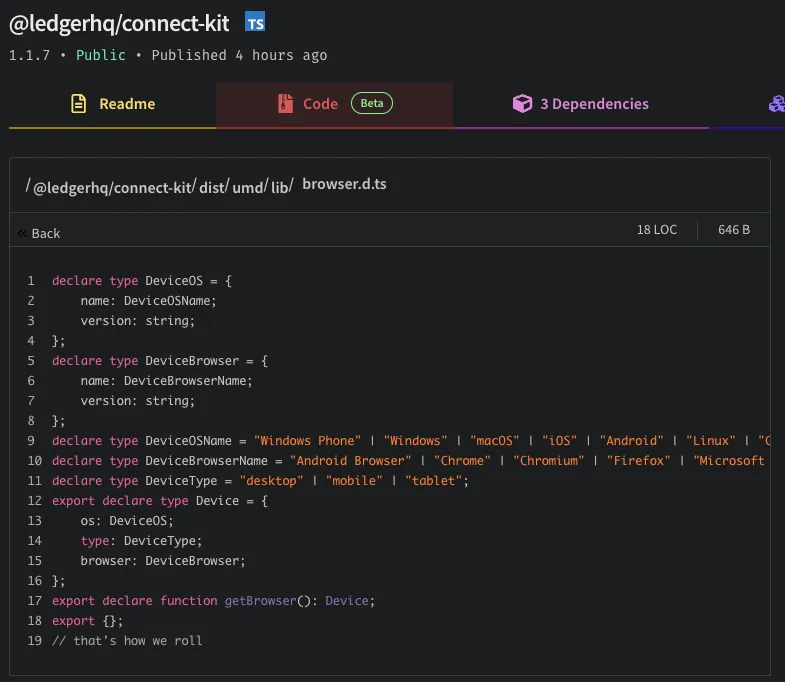
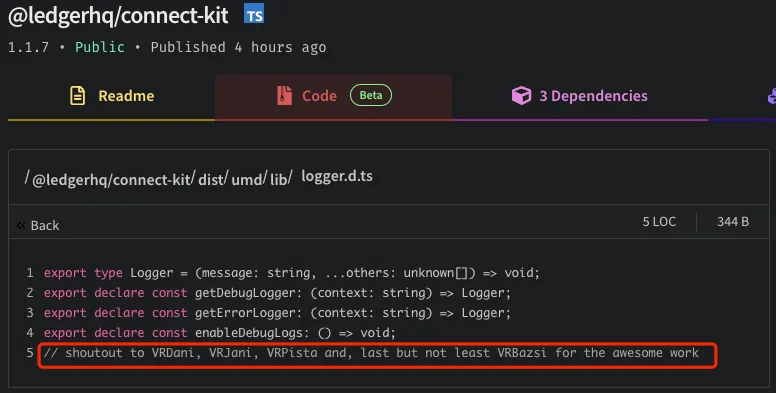
ledgerhq/connect-kit 1.1.7
Event Analysis
The Numen security team discovered that Ledger’s Ledgerhq/connect-kit module has been implanted with malicious phishing code, and that a large number of dapps integrate this functionality, with no clear statistics on the list of affected dapps, which is extremely wide-ranging.
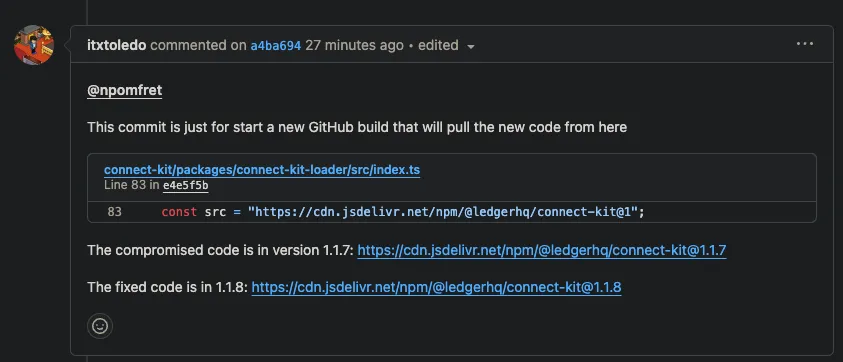
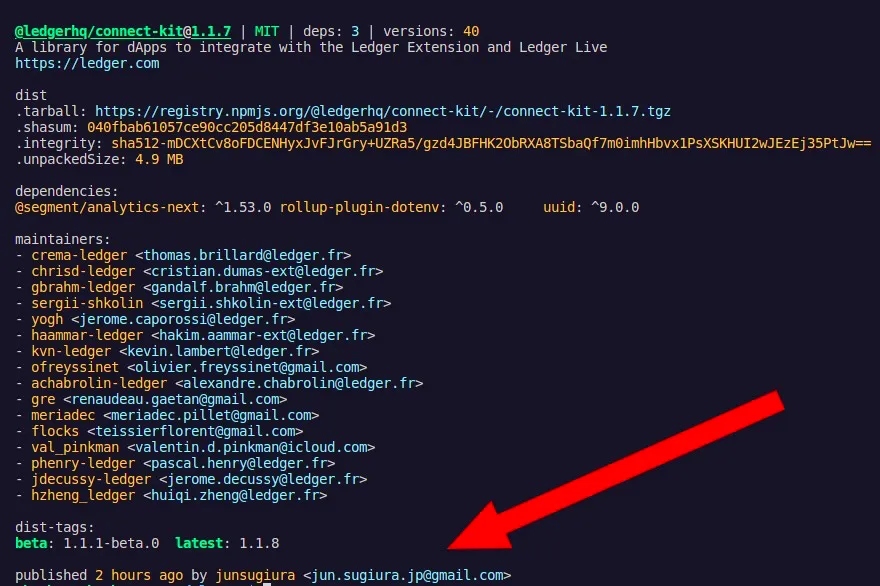
Poisoned code https://www.npmjs.com/package/@ledgerhq/connect-kit/v/1.1.7?activeTab=code
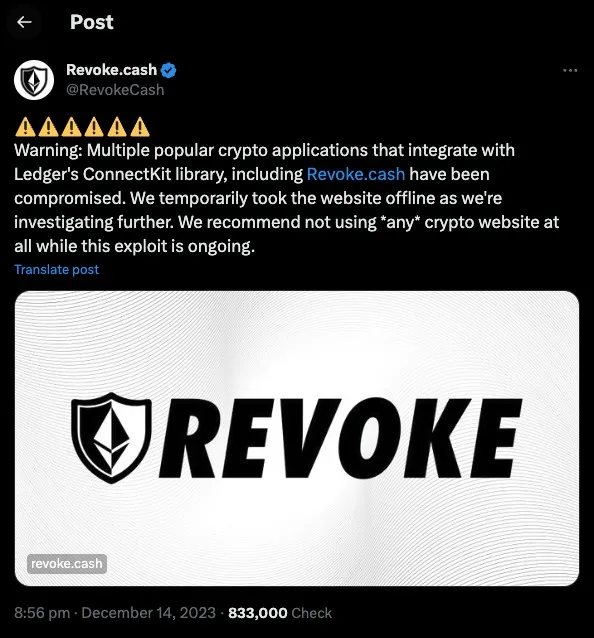
The Revoke.cash Dapp also integrates the Ledgerhq connect-kit (a security tool for managing wallet token authorizations and signatures).
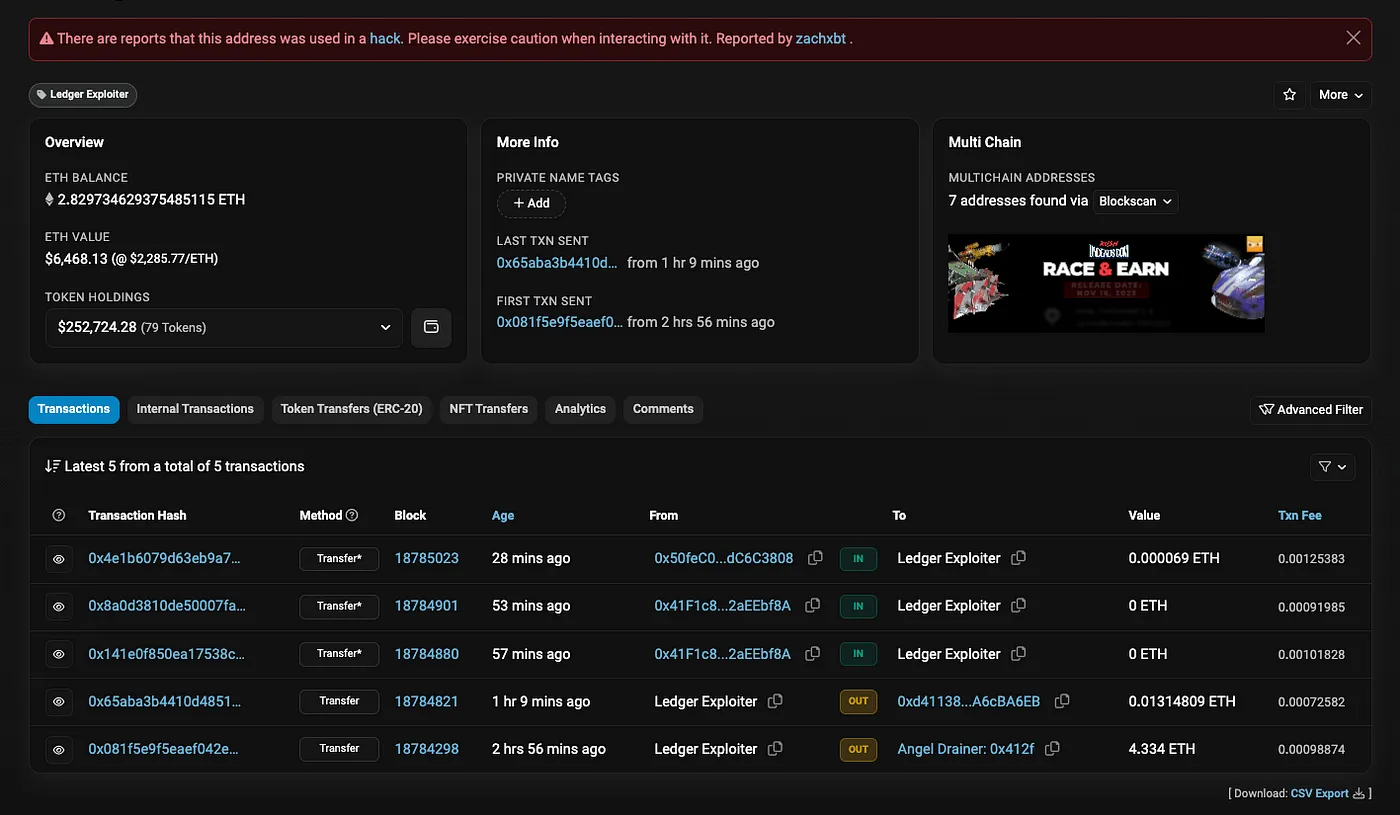
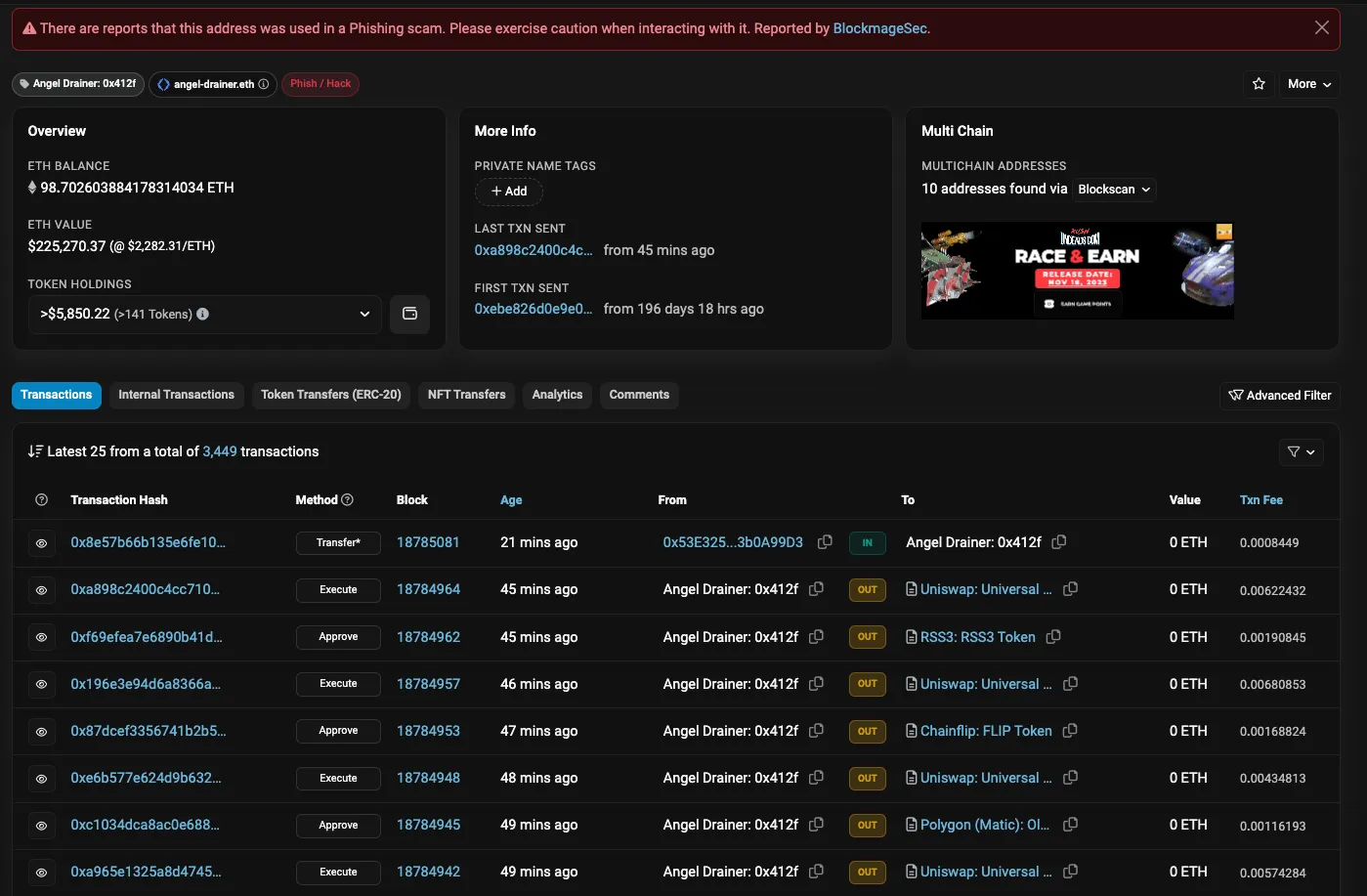
As of this posting, the hacker associated with the Ledgerhq Connect Kit incident has profited.
Hacked wallet address, associated wallet has been flagged.
The official fix has been pushed to https://github.com/LedgerHQ/connect-kit/releases/tag/ck-v1.1.8, until then please do not use your wallet to interact with any dapps for the time being.

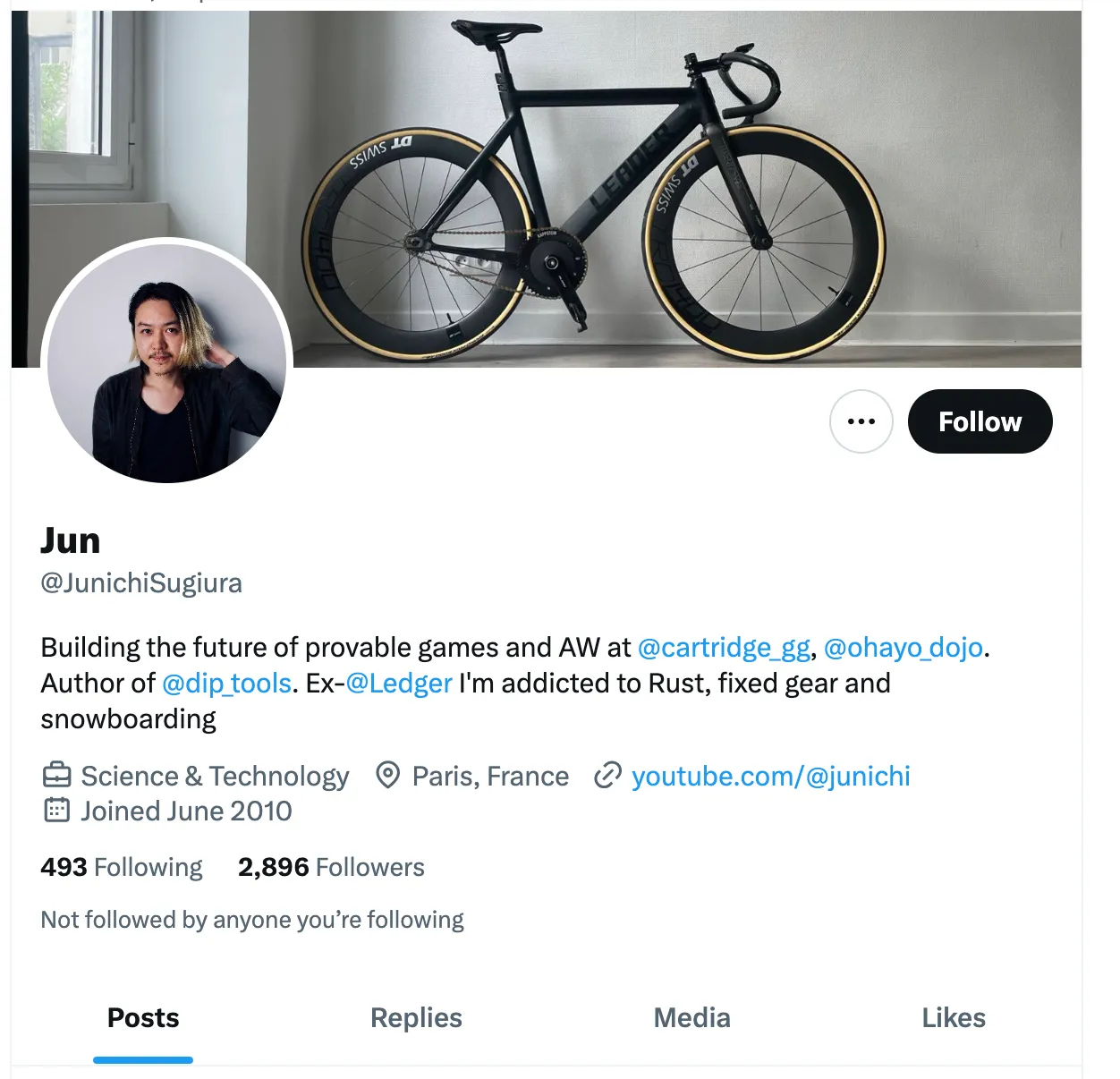
Attackers used this account when pushing code: @JunichiSugiura (Jun, former Ledger employee) jun.sugiura.jp#gmail.com, probably @JunichiSugiura’s account has been hacked.
summarize
In this incident, the attacker gained access to the code push account of a former Ledger employee @JunichiSugiura (I can’t rule out that it was done by myself), and then pushed malicious phishing code into the ledgerhq/connect-kit library to carry out a supply chain attack to steal the user’s cryptoassets when the user interacts with the dapp. ledger’s influence is very strong, and the project side of the dapp apps with a dependency on the module is requested to upgrade it as soon as possible.



